Invasive Technology Disrupts the Everyday: Behavioural analytics trigger a consumer backlash

As a deluge of sensors, cameras and other embedded devices fill homes, offices, factories and public spaces there will be growing concern from citizens. As organisations begin storing greater volumes of personal data, adversarial threats will increasingly target devices that harvest and process behavioural information.
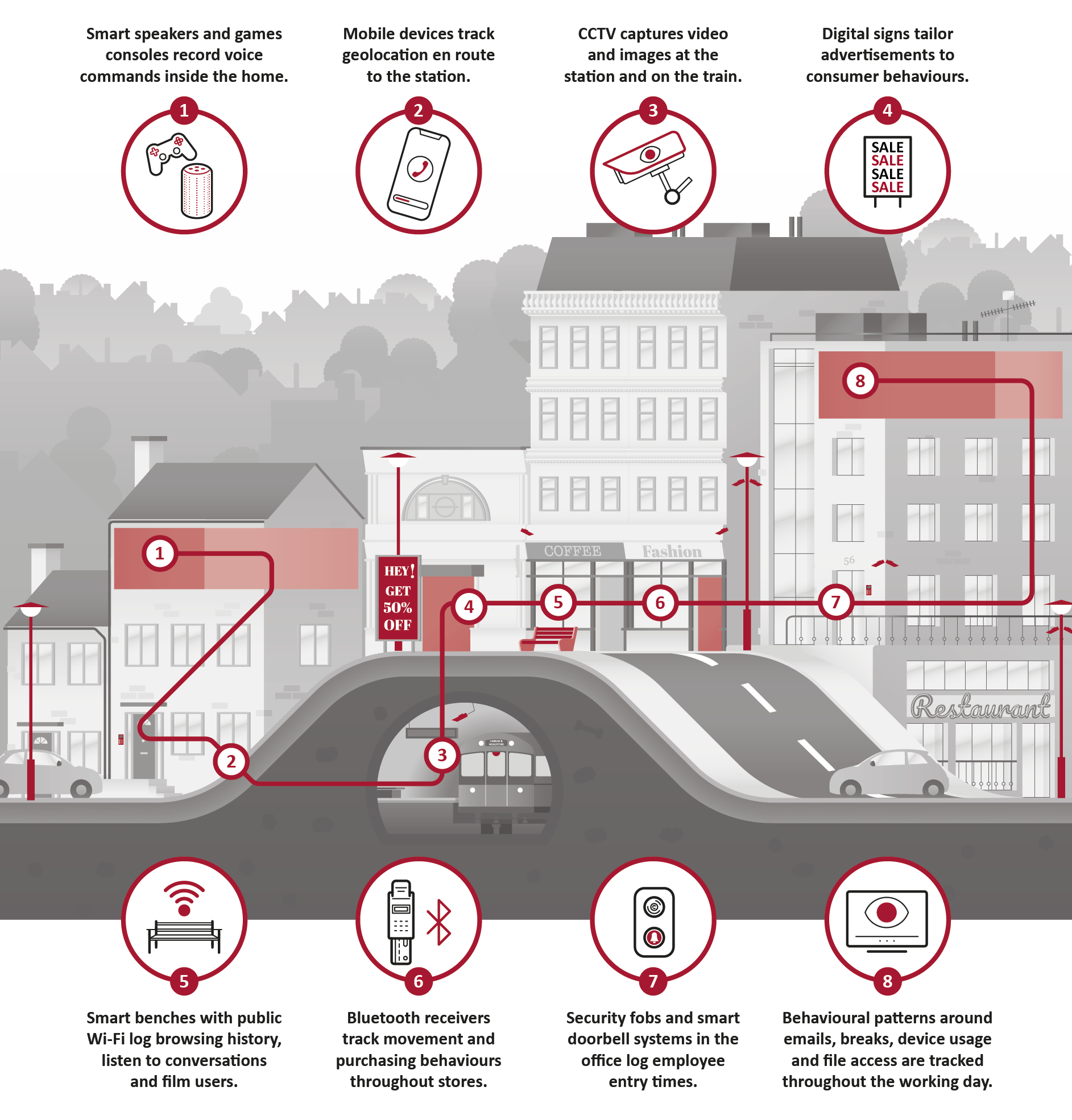
Behavioural analytics is a subset of big data analytics that is used to harvest, process, analyse and repurpose data into predictive behavioural information about consumers. By pulling data sets from multiple sources in both the digital and physical world, organisations are able to create profiles of individuals and groups that can be used to identify future trends and business opportunities.
A key factor in the growth of behavioural analytics is largely down to the number and volume of cameras, sensors and other IoT devices that have, and will continue to proliferate throughout private and public spaces.
Whilst this practice has the potential to offer organisations invaluable insight around consumer and non-consumer behaviours, it also stands to have rapid and dire implications if this treasure trove of data and information is misused or not properly secured.
Marketing and Advertising sector:
Organisations will begin utilising the data from sensors and cameras to create tailored content around marketing and advertising products. Behavioural analytics will create ‘data doubles’ as organisations use behavioural analytics in marketing and advertising campaigns that heavily tailor customer experience, products and services around these big data models. Everything from favourite brands, to spending habits, travel movements, and consumer attention will be tracked, recorded and consumed as organisations attempt to build up material perfectly tailored for ‘the market of one’.
- The increasingly invasive nature of data captured through behavioural analytics will prompt growing concern from the public and regulators. As the public and workforces begin to question monitoring practices and become aware of the frequency and volume at which these invasive practices occur, there is the potential to see widespread backlash against the use of behavioural analytics, with significant financial implications for dependent organisations.
- As organisations amass a treasure trove of data on their consumers and workforces, attackers will begin to target the vast networks of IoT devices due to their inherently low level of security and host of vulnerabilities. These soft targets will allow attackers to create back doors into networks and begin harvesting information about people that they didn’t even know about themselves.
This blog is one part in a series of blogs based on the Threat Horizon 2022 report. In the coming weeks, we will be discussing the three themes and nine threats covered in the report.
Find out more about Threat Horizon 2022: Digital and Physical Worlds collied here >
ISF Members can download the Threat Horizon 2022: Digital and physical worlds collide report here.
